Table of Contents
In this blog post, we would like to continue our discussion about the panacea for mission-critical application QoE issues.
Since analogies from the actual world of traffic to the world of IT network traffic serve us well to explain the pains and optional solutions, we’ll continue to use them in this blog post.
In the real traffic world, a traffic jam happens due to one or more of the following reasons:
- Road capacity does not succeed in containing the number of vehicles
- Traffic lights are not appropriately tuned to reflect the dynamic changes in traffic load during the day hours and days in the week
- An unplanned event such as an accident occurred and blocked the entire road
- Drivers do not respect driving rules, such as entering an occupied intersection
In a very similar way, traffic congestion that affects your mission-critical application QoE happens in organizational IT networks due to one or more of the following reasons:
- Data load exceeds existing bandwidth infrastructure
- IT traffic policy enforcement rules are not well-tuned to reflect the dynamic use of the IT network during working hours and days in the week
- An unplanned event creates an exceptional use of the network
- Employees do not respect network usage rules – for example, activating recreational applications during working hours
In both cases, as discussed in our previous blog post about bandwidth issues & challenges in relation to mission-critical application QoE, the consensus is that adding more infrastructure and bandwidth does not solve the congestion problem. IT traffic management has a lot more to do to successfully cope with the other challenges.
A couple of years ago, Google’s Director of Customer Reliability Engineering, Luke Stone, explained some of the major reasons for downtime and how developers and IT can address them. One of the top reasons he refers to is the “noisy neighbor.” Network users and all it takes is a few, bring spam or bandwidth-eating applications to work and become “noisy neighbors.” As a result, normal users throughout the enterprise are unfairly affected.
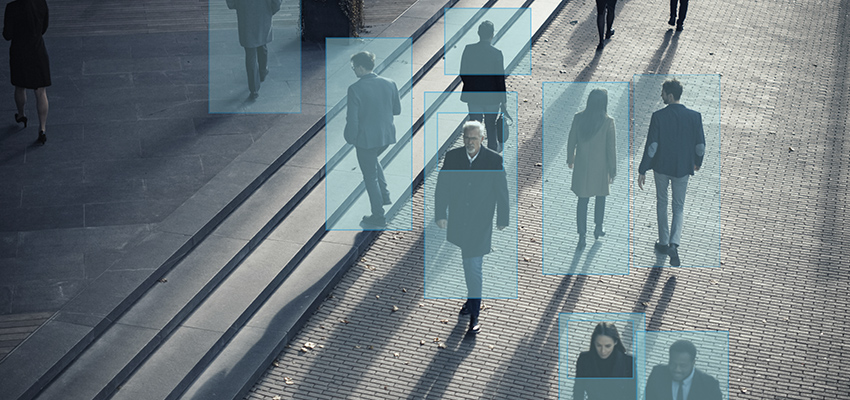
So, to minimize the “noisy neighbor” spam traffic, you must gain deep insight into your users’ network use. This deep insight is the real panacea.
What do we mean by “deep insight” into users’ use of the network?
Let’s take, for example, the use of a collaboration application. In today’s working world, these applications are considered mission-critical applications in many organizations. They are used for a few purposes, such as chat, and file transfer, as well as video and speech communications. These are the various user’s intents while using these applications. Each one of them requires a different network policy – in a chat of file transfer use, a little delay can be allowed, and the QoE will still be considered as good, while no delay can be allowed in speech and video use for optimized QoE.
Understanding user intent while using the network and applications is the deep insight you need to gain to fine-tune the policy rules and dynamically and smartly divide the existing network infrastructure so your users will get the optimized QoE for your mission-critical applications.
The Allot Traffic Intelligence Solution is a real-time networking device deployed at the organization’s data center network perimeter or cloud with a mission to understand the data, classify it to the specific application usage, and enforce the correct policy to assure mission-critical application QoE and continuity.
Understanding the data and classifying it may be challenging as IT professionals have various tools and techniques to achieve that. One option can be to deploy an agent on each organization’s endpoints and network traffic monitor activities. Such a technique will provide complete visibility into user activities but will introduce a blind spot for legacy, unmanaged, or IoT devices that can’t be installed with the monitoring agent. Additionally, deploying a network-based policy will be a bit more complex as the endpoint agent must communicate with the perimeter networking device and perform optimization ad hoc.
Secure Web Gateway (SWG) can also classify traffic and perform optimization. However, deploying SWG may also be challenging for local deployments since there is a need to push certificates to the entire endpoint to perform SSL inspection. Alternatively, using always-on cloud SWG requires changes on all network connectivity to be passed via the cloud SWG, which may introduce latency and QoE issues.
Next-Generation firewalls are composed of application visibility capabilities. When activated, they may consume lots of the firewall’s resources, often resulting in a more costly firewall. Hence, you will usually want a firewall to focus on its main function, which is to secure the network, and not on application optimization.
Allot provides Traffic Intelligence solutions that focus on only this aspect of the network. Since Allot is typically deployed inline, we see all network traffic, analyze it, and use powerful detection logic techniques to classify the traffic according to the specific applications in use and user intent. Allot Traffic Intelligence Solutions do not perform complex man-in-the-middle (MITM) SSL inspection or deploy agents on endpoints. The data is classified to provide IT managers with 360⁰ granular visibility of network use and user behavior. Once data is properly classified with the granular application and sub-application usage, the Allot traffic Intelligence solution can enforce any required policy to assure mission-critical application QoE, block traffic to malicious sites, stop shadow IT and unsanctioned application usage, and enforce policies on unmanaged and IoT devices relying on the egress/ingress of network traffic.


 What is ZuoRAT?
What is ZuoRAT? A look back at Infosecurity 2022
A look back at Infosecurity 2022 Do we really need 5G?
Do we really need 5G?


